Common Mistakes When Running Multiple Accounts in Antidetect Browsers
Blog » Common Mistakes When Running Multiple Accounts in Antidetect Browsers
Today multiaccounting is used not only in affiliate marketing and advertising, but also across e-commerce, SMM, recruiting and many other fields. At the same time, antifraud systems are becoming more sophisticated. Platforms compete to ensure 🕵️ user uniqueness and analyze not just IP addresses, but also device fingerprints and behavioral patterns to detect linked accounts. In most cases, detection and bans don’t happen because of multiaccounting itself, but because of setup mistakes.
The core issue is that many users treat an antidetect browser as a universal solution: create profiles, launch them… and that’s it. But the reality is different: IP overlaps, fingerprint matches, reused consumables, incorrect proxy assignment, unnatural behavior and geo mismatches leave strong signals. Today, we’ll discover the 🔎 most common multiaccounting mistakes and explain how platforms actually detect them.
How Platforms Detect Multiaccounting
Modern antifraud systems have moved far beyond simple IP checks. Today multiaccounting detection is built on correlating a wide range of signals: technical environment parameters, network data, behavioral patterns and relationships between accounts. Even if individual signals look clean on their own, their combination almost always forms a unique user profile. That’s why multiaccounting is typically uncoveded when the same data sets overlap across multiple accounts.
What Platforms Analyze 🤔
Platforms perform a comprehensive assessment of each user to build a consistent digital identity. The key analysis vectors include:
![]()
Pixelscan is a popular service for checking browser and device fingerprints.
🌏 IP and geolocation. Platforms assess not just the IP address itself, but also its type, reputation, usage history and alignment with the account’s claimed geography. They look at IP ranges, rotation frequency, overlaps between accounts and network type. If multiple accounts repeatedly log in from the same IP pool or abruptly switch countries, the system clusters them together.
🦶 Digital fingerprint. This includes dozens of parameters: user agent, WebGL, Canvas, fonts, screen resolution, audio stack, timezone, hardware specs and their internal consistency. Antifraud systems evaluate not only exact matches but also how rare the overall combination is. If several accounts share an identical or statistically unusual fingerprint, that’s a strong signal for closer scrutiny.
🤸♂️ Behavioral patterns. Platforms analyze action dynamics: click speed, page sequences, timing, registration and ad-launch flows, and time-of-day activity cycles. Even with different IPs and devices, identical workflows like mass account creation followed by rapid campaign launches create an operator-level behavioral signature.
👯 Account linkage. Platforms map relationships between accounts: emails, phone numbers, domains, tracking pixels, payment methods, business managers, devices, cookies and IP pools. Reusing even a single element or indirect overlaps between them gradually ties the entire network together.
Differences in Platform Approaches
Advertising platforms invest heavily in 🔐 protection algorithms because their revenue depends on user uniqueness and the integrity of ad delivery. However, their approaches to detecting multiaccounting differ.
For example, Google relies on broad, system-level signals: accounts, devices, cookies, cross-service behavior, payments and activity history. In advertising, trust in the advertiser and billing setup is critical: reusing payment credentials or domain infrastructure quickly links accounts together.
For a deeper dive into multiaccounting in Google Ads, read here.
TikTok, Facebook, and other social networks, in contrast, focus on social and behavioral linkage: interaction graphs, devices, sessions, IP clusters, and business structures (Business Managers, pages, pixels). Their systems are particularly effective at uncovering account networks operated by a single actor even when they’re segmented with proxies and isolated browser profiles.
For a deeper dive into multiaccounting in TikTok, read here.
In e-commerce, marketplaces prioritize commercial signals: seller identities, listings, payments, addresses, logistics data and login devices. Many enforce a strict “one seller — one account” policy, so overlaps in documents, payment details or operational activity can lead to the suspension of an entire linked network of storefronts.
For a deeper dive into multiaccounting in Amazon, read here.
At the same time, they never disclose the exact reason why a user was banned. Revealing specific triggers, ban thresholds or detection methods would make it easier to bypass their antifraud systems.
Mistakes in Multiaccounting
Now we a ready to discuss the most common mistakes in multiaccounting: what exactly users do wrong, how platforms interpret it and what consequences it has in practice.
Mistake #1: Identical or Linked IPs
One of the most widespread issues in multiaccounting is using identical or related IP addresses across different accounts. This typically happens when an operator works without proxies, sources proxies from the same subnet, uses resold/shared IPs or runs multiple browser profiles through a single proxy.
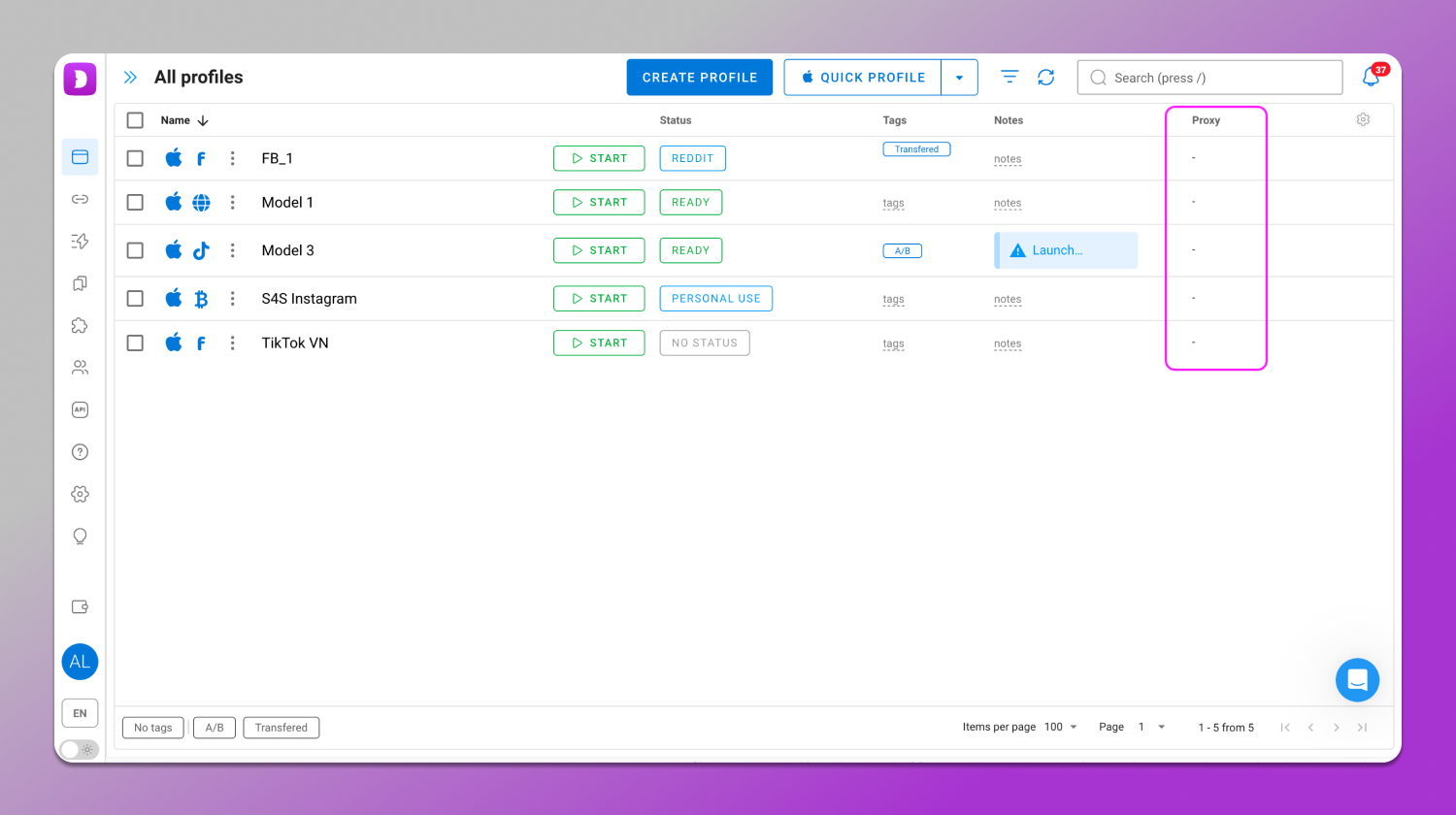
These accounts are launched from the same IP without proxies.
Anti-fraud systems don’t treat an IP as an isolated signal as they evaluate its network context. If multiple accounts consistently appear from the same pool or adjacent subnets, an IP cluster is formed. Even without simultaneous logins, the system can see that the accounts exist within the same network environment.
The moment when a platform links accounts by IP, it rises to the group level rather than a single profile. Trust may degrade first: feature limits, verification checks, moderation delays. Then after any violation or just suspicion not single account but the entire linked cluster can be suspended including those with no direct infractions. In practice, this means losing ad accounts, active campaigns, working profiles and attached assets. Relaunching from the same IP environment often leads to an instant re-ban.
Mistake #2: Improper Proxy Usage
Another common mistake is that any residential or static proxy is automatically safe for multiaccounting. In practice, proxy quality isn’t defined by the label type but by the IP’s origin, usage history, pool size and how natural the surrounding network environment appears. As a result, even with formally unique IPs accounts can still face restrictions or bans because their IP footprint looks atypical for normal user traffic.
Running multiple accounts through the same proxy is also not recommended.
Antifraud systems evaluate IPs in a comprehensive way: network type, range reputation, activity history, rotation frequency, geo alignment and connection stability. If IPs come from a narrow or heavily used pool, frequently change region or ISP, show atypical latency or were previously used at scale, the system 📉 lowers the account’s trust score. Even without direct overlaps between profiles, these signals indicate logins via proxy infrastructure rather than a normal consumer network.
Typical proxy configuration mistakes include:
- Overly precise geo targeting that shrinks the available IP pool;
- Reassignment of previously used or burned IPs;
- IP overlaps between accounts during rotation;
- Abrupt ISP or region changes between sessions;
- High latency or unstable speeds atypical for real users.
Unlike direct IP overlaps, this scenario usually degrades the trust of each account individually rather than linking the entire network at once. In practice it leads to extra verification checks, limits, moderation rejections or reduced trust in payments and ads. As suspicious signals accumulate, the account may eventually be suspended.
Mistake #3: Cloned Digital Fingerprints
Mass cloning of browser profiles is a common scaling tactic when a single golden profile is created and then duplicated with minimal changes. As a result, accounts end up sharing nearly identical fingerprint parameters. These profiles appear virtually indistinguishable to antifraud systems.
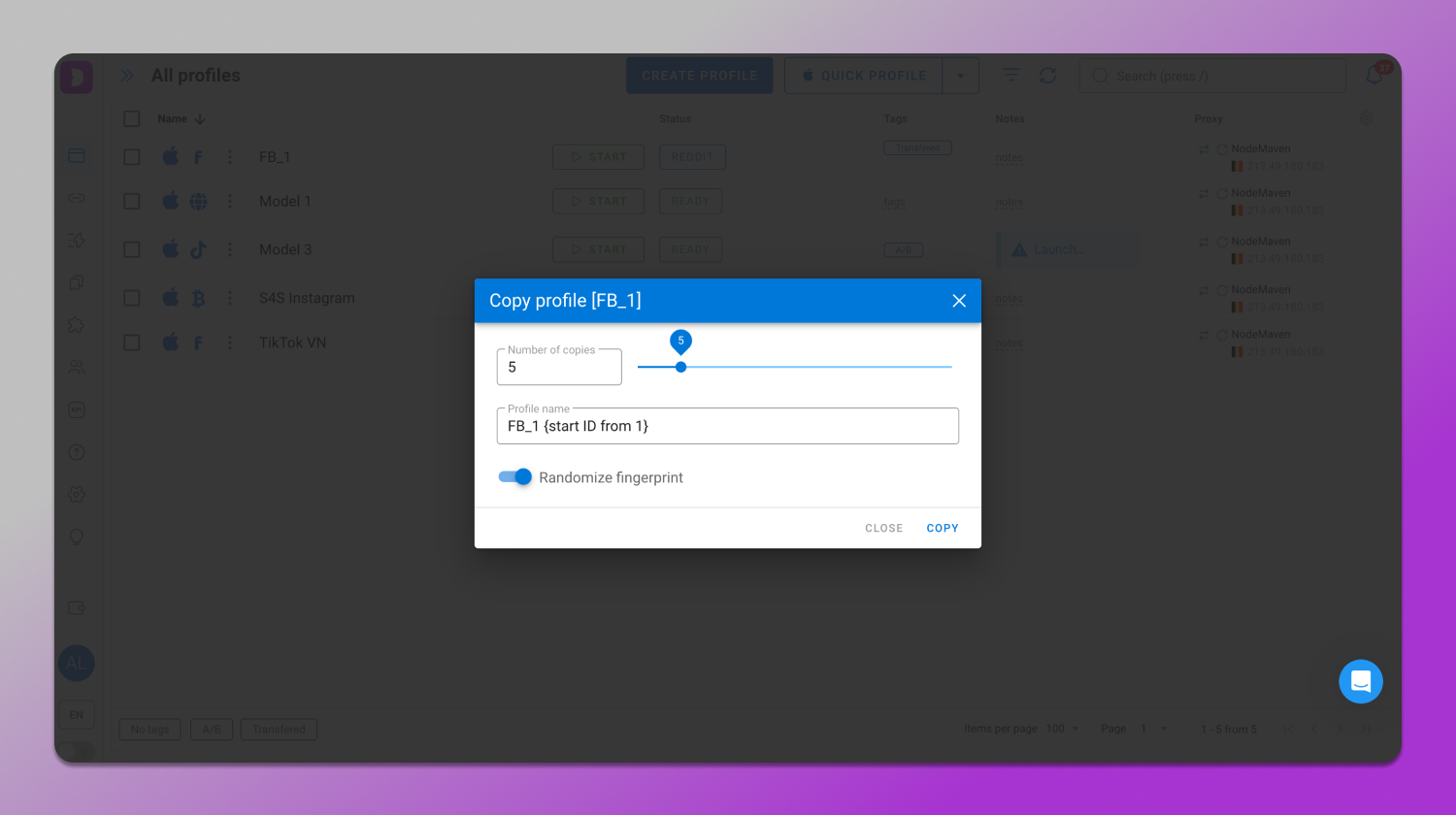
When duplicating profiles in Dolphin Anty, it’s best to randomize the fingerprint.
A fingerprint contains dozens of interdependent parameters: user agent, screen resolution, WebGL/Canvas signatures, fonts, audio stack, timezone, language, hardware specs and their internal consistency. When multiple accounts share an identical or statistically rare combination, the system quickly links them. Minor changes don’t help here, because antifraud evaluates the environment as a coherent whole.
Unlike IP or proxy signals, a fingerprint is analyzed 🪄 instantly. It doesn’t require usage history and any matches are detected at first launch. Moreover, cloned profiles tend to evolve in lockstep (browser, font or OS updates), further confirming a shared origin. That’s why mass‑copied profiles often get banned in batches early in their lifecycle before any serious ad activity even begins.
Mistake #4: Similar Account Behavior
Even with unique IPs and fingerprints, accounts are often ⚙️ operated using the same playbook: identical action sequences, timings and intervals between steps. This commonly happens with automation, when accounts are registered, warmed up and launched following the same template.
To detect multiaccounting, platforms build behavioral profiles: click speed, browsing depth, page sequences, step duration, time‑of‑day activity and responses to UI elements. These signals form a behavioral model of how a specific user interacts with the system. When multiple accounts exhibit matching workflows, algorithms link them even without any technical overlaps.
Real users behave in a chaotic way: they vary pace, get distracted, make redundant clicks or detours. When dozens of accounts act too synchronously or too consistently, their trust drops sharply. As a result, platforms may flag them for review or suspend clusters of profiles connected by a shared behavioral graph.
Mistake #5: Reusing Consumables
In multiaccounting consumables refer to all supporting assets: accounts, emails, phone numbers, payment methods and similar identifiers. The typical mistake is reusing them across different accounts or creating indirect overlaps. The most common cases are the same 💳 card used in multiple ad accounts or a single phone number reused for verification. Even with unique technical environments and IPs, these matches directly link accounts at the billing layer.
Platforms build 🔗 trust chains around each account by aggregating payment methods, cardholder names, billing addresses, phone numbers, domains, legal entities and transaction history. These identifiers are highly valued in antifraud because they’re the most persistent. Repetition of any element or cross‑linking via payments, confirmations or shared credentials automatically clusters accounts together regardless of device or IP.
Linkage through consumables is one of the most severe detection types. If one account is sanctioned, restrictions often cascade to all associated accounts and payment methods. In practice, this leads to ad account suspensions, payment declines, failed verifications and loss of the entire connected infrastructure.
Examples of Account Suspensions by Major Platforms
On forums like Reddit, users often discuss ad‑platform account bans. Here are a few illustrative cases.
Case #1: One Credit Card Across Two Ad Accounts
An advertiser created a new Google Ads account for a client but added the same credit card that had already been used in another ad account. Within a few days, the new account was suspended by Google with the notice “suspicious payment activity”. It later became clear that using the same card across multiple accounts can be treated by the system as a signal of multiaccounting and restriction evasion.
Case #2: Multiple Accounts Suspended for Policy Circumvention
A user was managing several Google Ads accounts. At one point, 5 out of 7 were suspended simultaneously. Google cited “circumventing systems” as the reason. The platform determined that the accounts were somehow linked via IP, devices, payment data or behavioral signals even though they appeared as separate profiles on the surface.
The suspension was triggered automatically without support review. Later they advised filing an appeal but offered no guarantee of reinstatement. The user concluded that the platform’s algorithms correlate accounts across multiple signals and that maintaining several linked accounts significantly increases the risk of a synchronized group‑level suspension.
Case #3: Meta Ad Account Suspension
A user faced a long-term suspension of their Meta ad account. The notification cited violations of advertising standards: too many disapproved ads, attempts to bypass ad review and connections to untrustworthy accounts.
As a result, strict restrictions were imposed:
- Unable to create or run ads;
- Cannot use or share audiences;
- Meta Pixel and tools for tracking custom or offline conversions became unavailable;
- Event submission via App SDK was blocked.
Attempts to contact support were unsuccessful and the appeal option through the interface was unavailable. This illustrates that accounts can be suspended based on a combination of signals including ad quality, rejection history and links to other accounts.
How Dolphin Anty Reduces Detection Risk
Most multiaccounting mistakes stem from ☝️ overlaps and environmental inconsistencies: conflicting device parameters, repeated fingerprints, IP intersections and unnatural behavior. The antidetect browser 🚀 Dolphin Anty mitigates these risks through a comprehensive approach to profile creation.
Profile Isolation and Consistency
Each profile is created as a fully isolated environment with internally consistent device and browser parameters that closely match real user configurations. The system checks them for logical contradictions and flags potential risks, for example, if the selected OS doesn’t align with the host device’s actual platform.
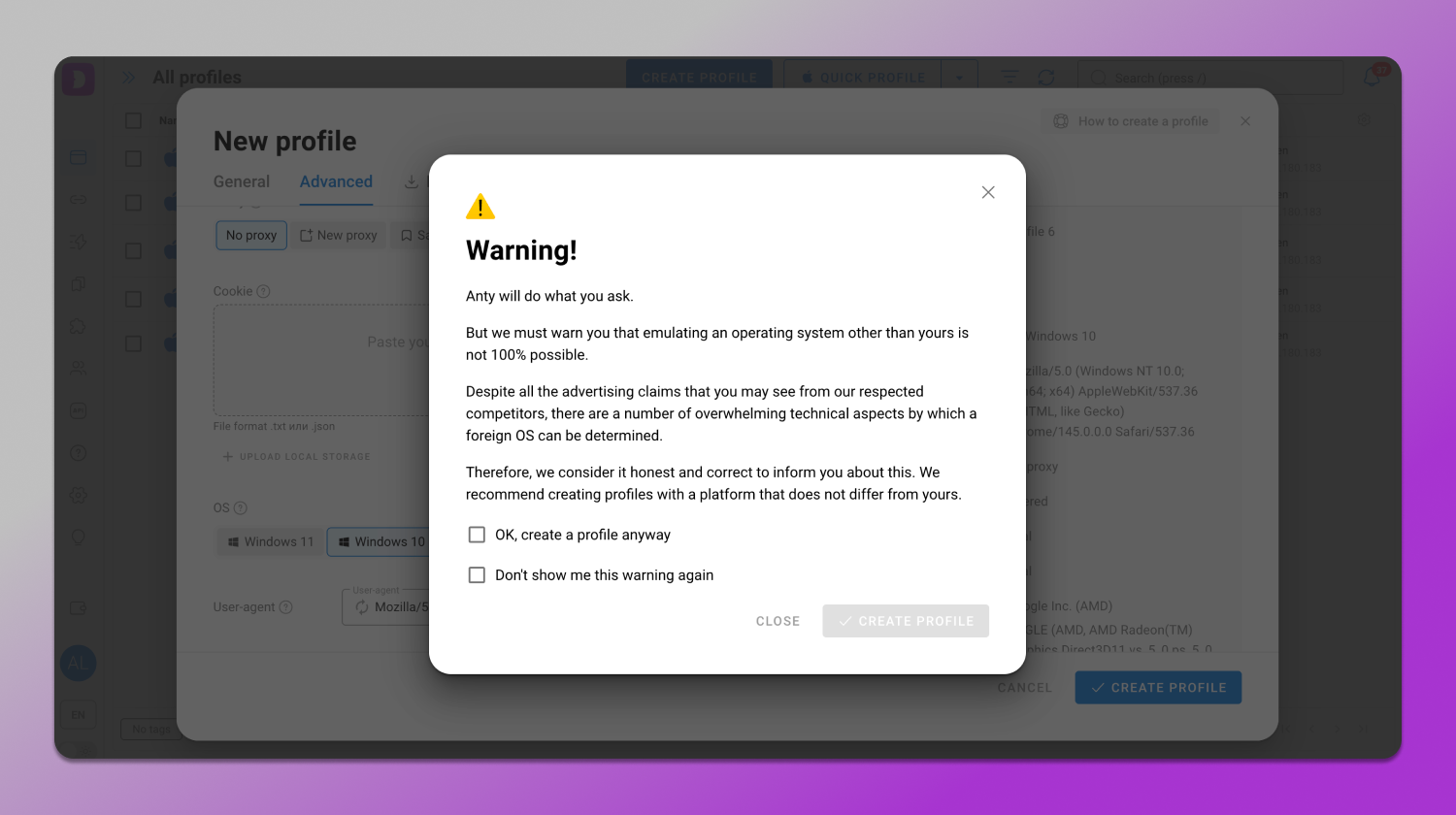
All of this reduces the likelihood of generating suspicious fingerprints.
Digital Fingerprint Management
Profiles can be configured both ⚙️ automatically and 🛠 manually when precise parameter control is required. The interface provides contextual guidance and safeguards to help maintain a natural, realistic environment.
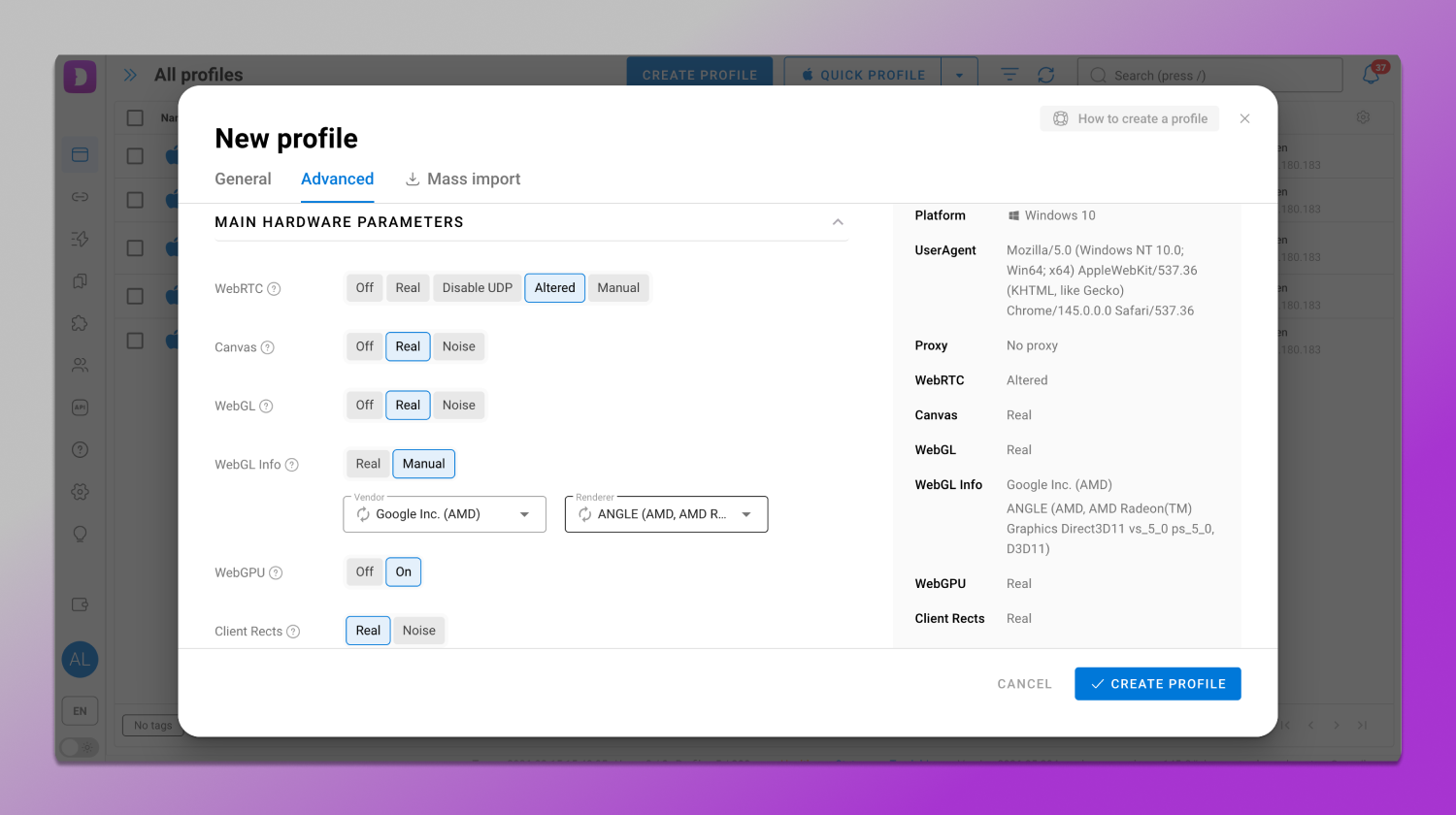
As a result, even with randomization, the fingerprint remains statistically plausible and stable.
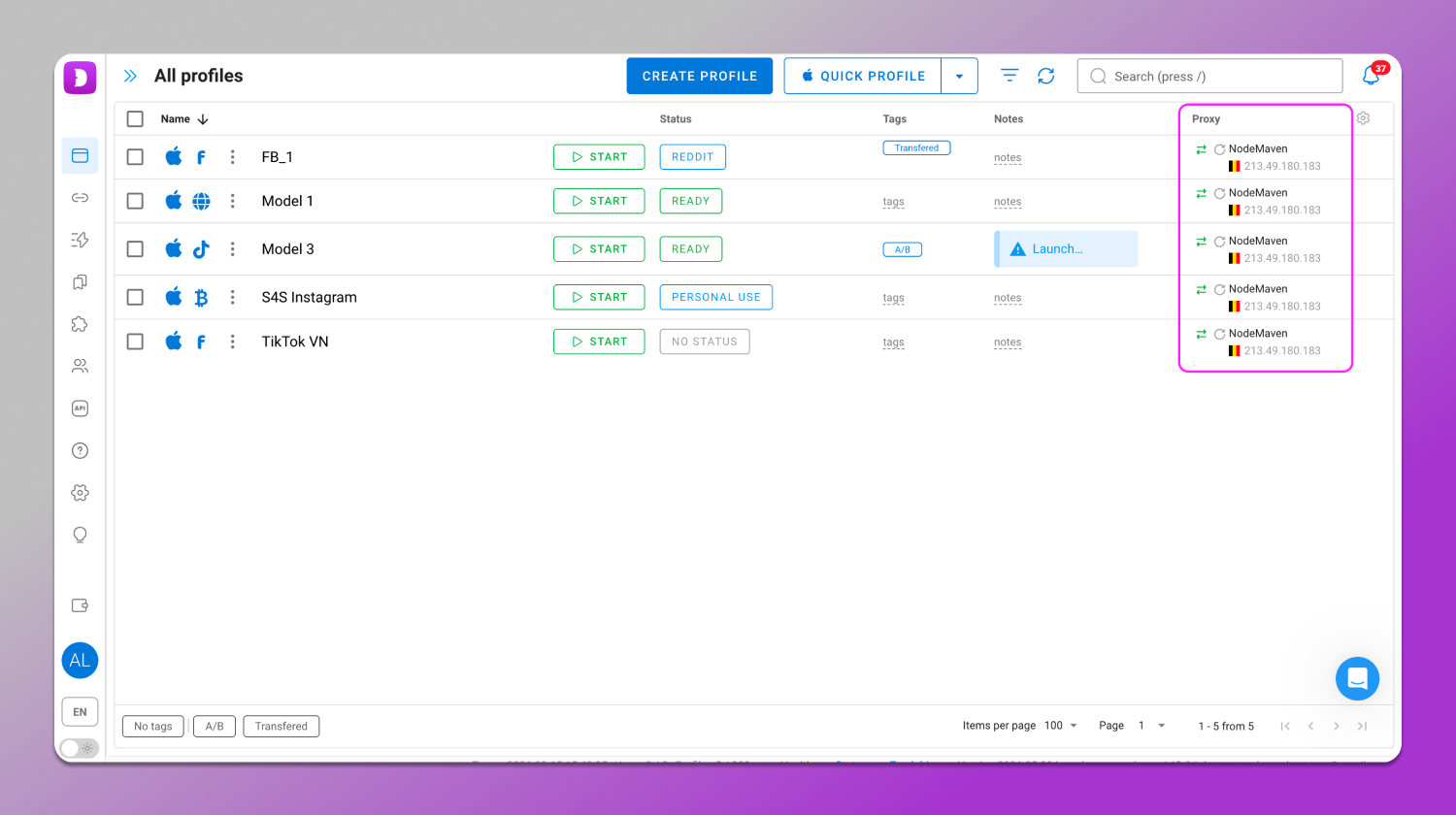
Proxy
Proxies can be attached to profiles individually or in bulk and assigned automatically or manually without overlaps between accounts.
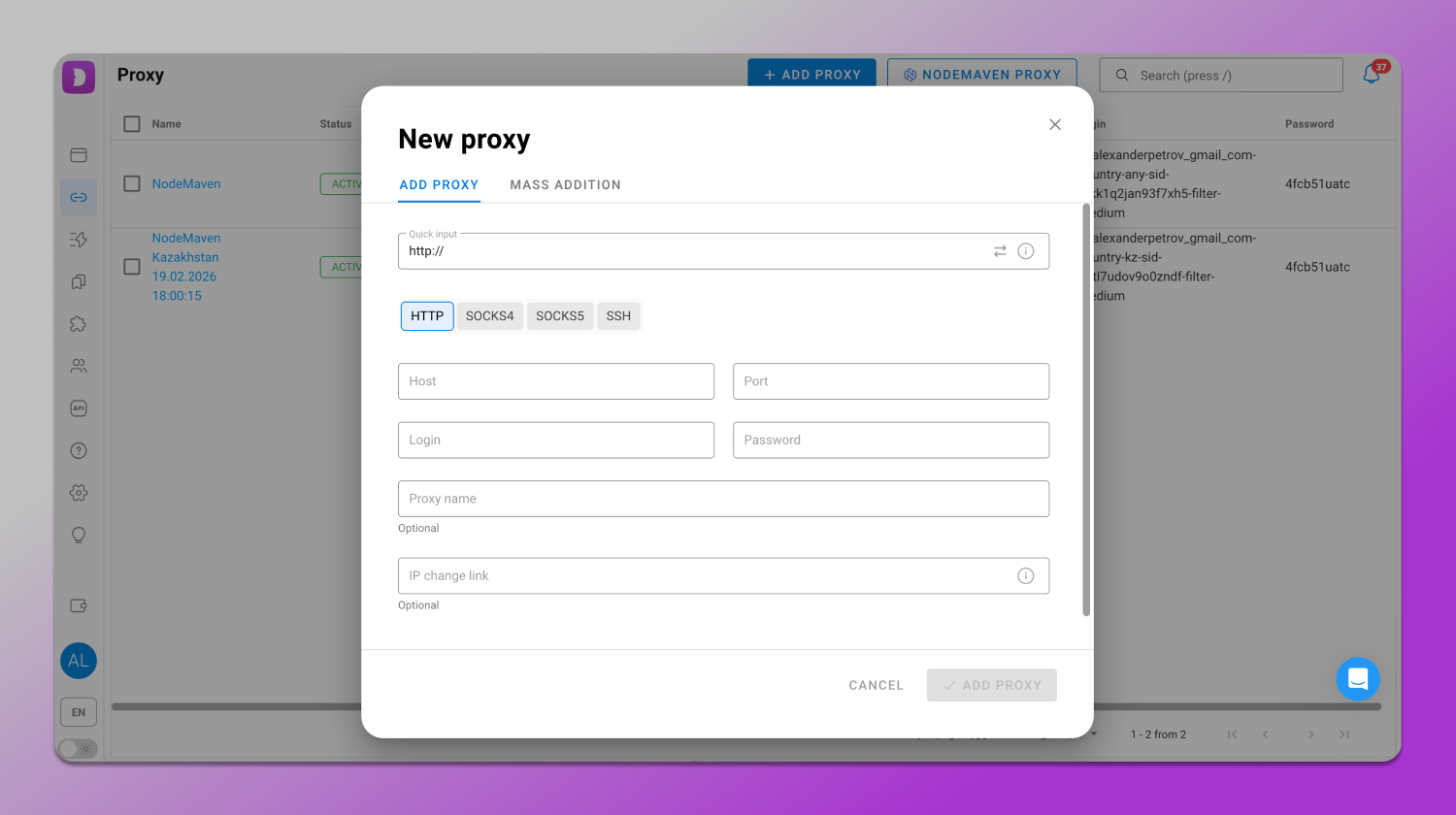
Different proxy types are supported along with integrations with providers that supply high‑quality IPs only.
Smart Automation
Dolphin Anty includes 🔁 automation tools designed to save time on repetitive actions.
The Cookie Robot lets you 🍪 collect cookies on specified websites in the background which is useful for account warm‑up. To improve speed and reduce proxy traffic usage image loading can also be blocked.
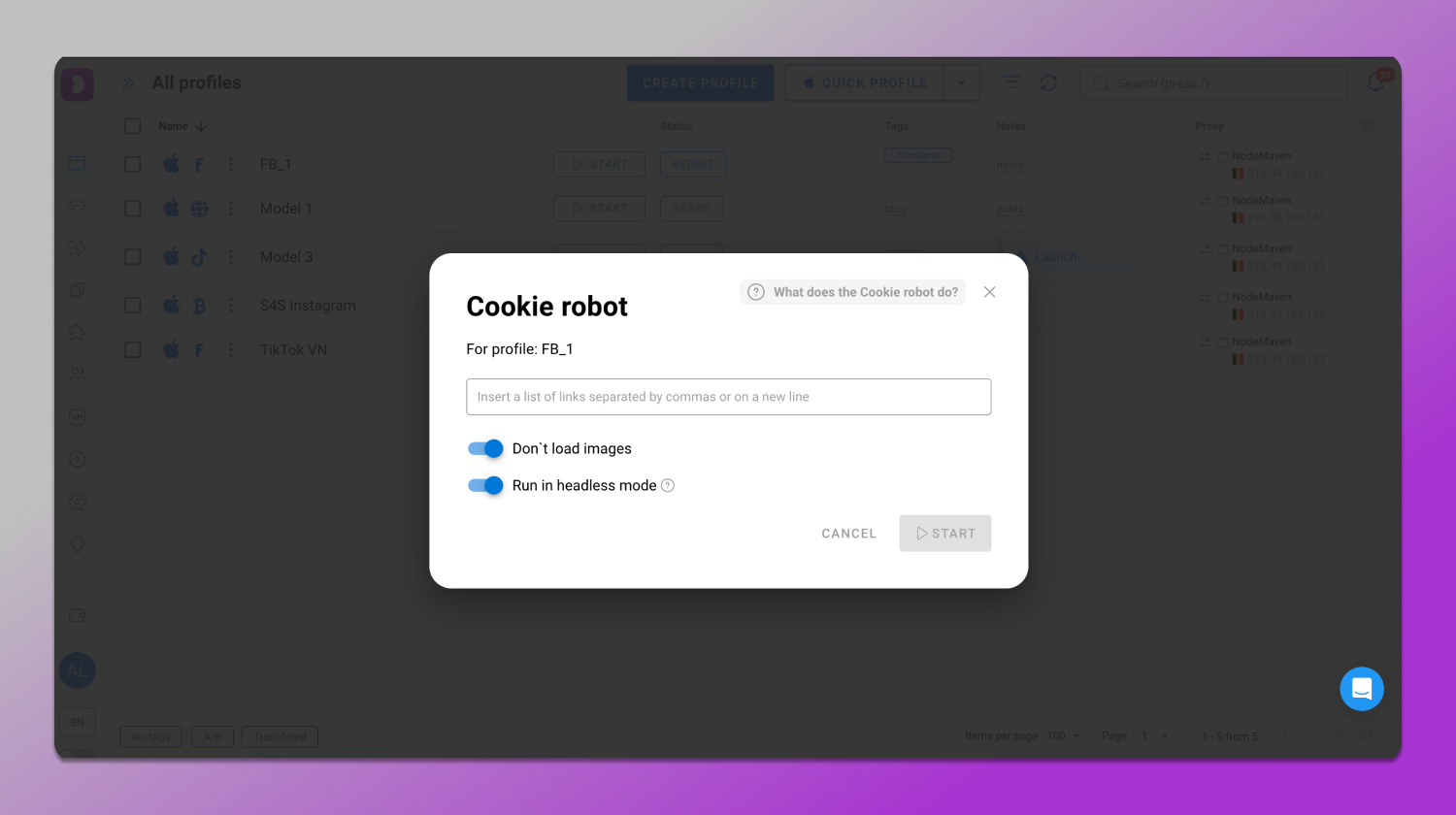
Scenarios are another automation tool. On an interactive map you can build action sequences like clicks, data entry, scrolling, opening sites in browser profiles without writing any code.
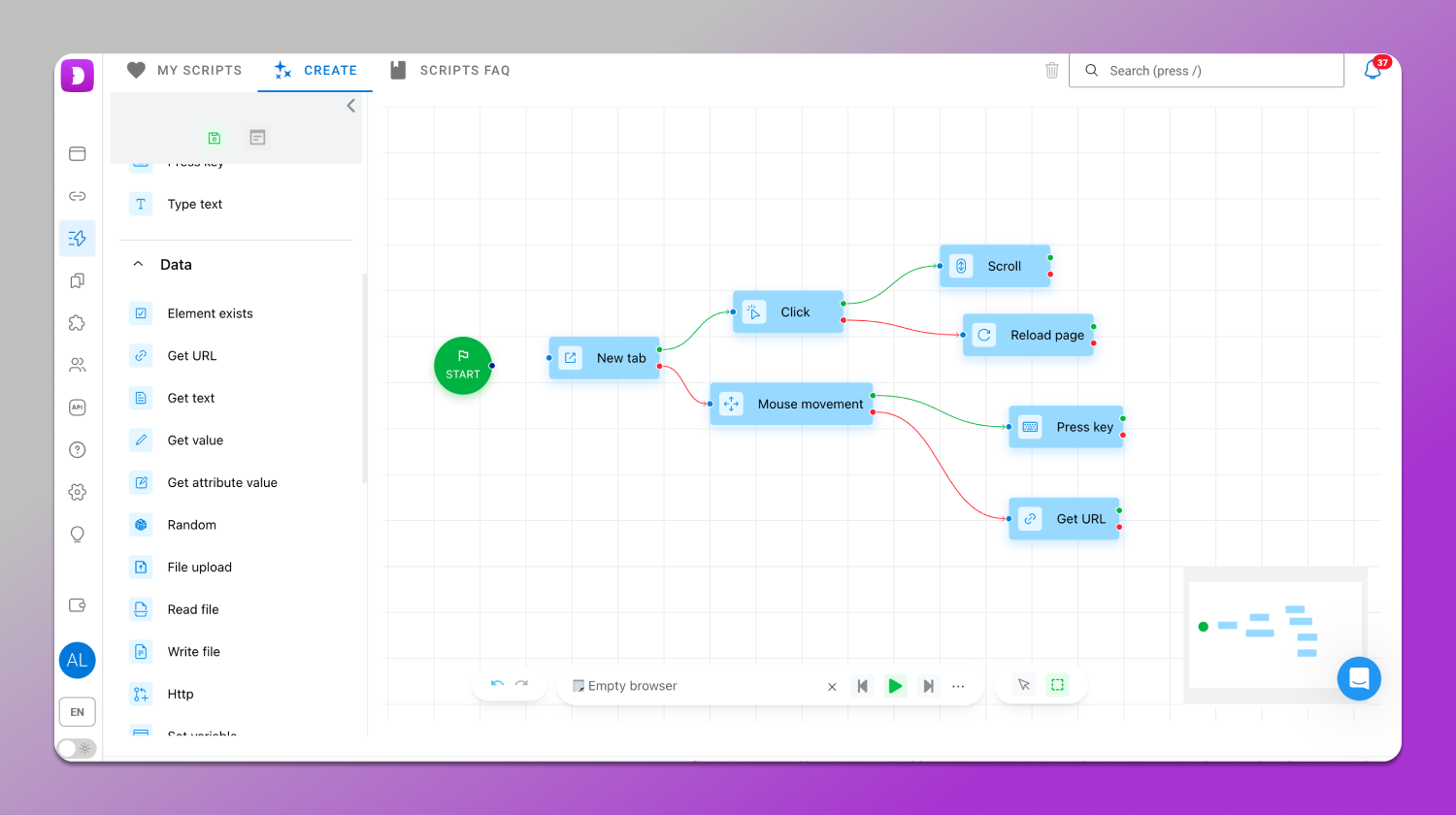
This helps with account farming, warm‑up, auto‑registration and ad operations. You can also share accounts with teammates.
Taken together these tools isolate accounts across the technical, network and behavioral layers. In these very dimensions platforms detect multiaccounting most often.
Conclusion
The primary cause of bans for multiaccounting isn’t the mere fact of running multiple accounts, but their linkage. Platforms don’t detect “multiaccounting” per se as they detect overlaps between profiles. The more touchpoints accounts share, the higher the chance they’ll be clustered together and restricted as a group.
To recap, here’s what ❌ not to do:
- Use identical or overlapping IPs;
- Operate within a narrow proxy pool;
- Mass‑clone profiles and fingerprints;
- Manage accounts with identical workflows;
- Reuse emails, phone numbers, payment methods or domains.
These risks can be minimized with a systematic approach to environment isolation and account management. 🔥 Dolphin Anty creates independent profiles, enforces fingerprint consistency, manages network environments and helps avoid overlaps and template‑like behavior. The result is account isolation and a significantly lower risk of group‑level bans. If multiaccounting is part of your operations, a properly configured environment isn’t just a helpful tool as it is a foundational infrastructure.